Copycat Websites: The Endless Mayfly Network
Overview
“Endless Mayfly” was an operation that created inauthentic spoofing established and online personas to spread false and inflammatory content targeting Saudi Arabia, the US, and Israel from at least April 2016 to November 2018.1 The operation astroturfed a false grassroots organization purporting to advocate against Saudi Arabia and Wahhabism, and seeded related false content to activists and journalists, which in some instances was traded up the chain to the mainstream media.
STAGE 1: Manipulation Campaign Planning and Origins
Mayflies are not actually flies at all. These insects can develop for years under the water, but once they hatch in their adult form they live only briefly — in some cases, a mere 5 minutes. Though they don’t last long, when they’re flying they’re hard to escape.2 An ephemeral and seemingly unending operation to impersonate mainstream websites and spread false information around the world from April 2016 to November 2018 was dubbed “Endless Mayfly” because it shared these characteristics. And just as mayflies are usually only seen near the end of their life-cycle, emerging from the water after months and years below the surface, the campaign of the same name was not observed by the press or internet researchers until it had reached Stage 2 in 2017.
What is known about the planning phase of the campaign is only that which can be inferred from the networked activities and consistency in tactics and narratives, which suggest the operation was likely planned, and possibly centrally controlled, in private spaces of the internet that are not accessible to researchers.
Ultimately, Endless Mayfly was attributed to an “Iran-aligned” group, though the attribution was made with only medium confidence. What is known, however, is that the narratives and messaging of the manipulation campaign framed Western countries, the Gulf states, and Israel in a consistently negative light, playing on wedge issues (ex. Gulf states’ cooperation with Israel) and diplomatic crises (ex. 2017 Qatar diplomatic crisis).3 Furthermore, the articles often targeted politicians or political parties within these countries.
- 1Gabrielle Lim, Etienne Maynier, John Scott-Railton, Alberto Fittarelli, Ned Moran, and Ron Deibert, “Burned After Reading: Endless Mayfly’s Ephemeral Campaign,” Citizen Lab, May 14, 2019, https://citizenlab.ca/2019/05/burned-after-reading-endless-mayflys-ephemeral-disinformation-campaign/.
- 2“Mayfly,” Wikipedia, accessed August 18, 2020, https://en.wikipedia.org/wiki/Mayfly.
- 3Lim et al., “Burned After Reading.” See “Part 2: Endless Mayfly’s Preferred Narratives.”
STAGE 2: Seeding Campaign Across Social Platforms and Web
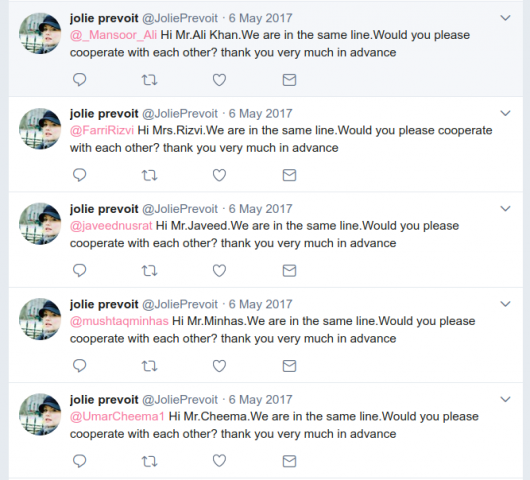
The earliest known activity attributed to Endless Mayfly is the creation of six Twitter personas from April 2016 to April 2017. The earliest account called itself “JoliePrevoit” and used a photo of actress Elisha Cuthbert as its profile picture.1 These personas claimed they were students, journalists, or activists and identified themselves as members of an organization calling itself the Peace, Security, and Justice Community (@PSJCommunity on ; see figure 1 below). This organization, along with the personas, promoted inauthentic articles and stories critical of Saudi Arabia on Twitter.2 There was no evidence the organization ever existed in real life, indicating the personas along with this purported organization were engaged in .3
- 1 Lim et al., “Burned After Reading.” See “Appendix A: Timeline of The Endless Mayfly Network.”
- 2Lim et al., “Burned After Reading.” See “Part 2: Endless Mayfly’s Preferred Narratives.”
- 3PSJ Community (@PSJCommunity), Twitter [account has since been deleted], https://web.archive.org/web/20181026193612/twitter.com/psjcommunity.
Figure 1: False organization linked to the network that primarily targeted Saudi Arabia. Twitter profile archived here: https://web.archive.org/web/20170122102233if_/https://twitter.com/psjco….
During this time (April 2016 - April 2017), the personas tweeted links to inauthentic articles, posted on other platforms like Reddit, and reached out to real individuals in a bid to disseminate their content (see figure 2 below for an example of one of the personas’ activity). For example, On April 5, 2017, a persona calling itself “Eliana Badawi” posted a link on to a website that looked like the UK-based media outlet, The Independent.1 Other redditors were quick to point out that the link employed typosquatting by pointing to indepnedent.co, as opposed to the real outlet’s URL, which is independent.co.uk. The inauthentic article contained false claims alleging that former Deputy Prime Minister of the U.K. Nick Clegg had accused then U.K. Prime Minister Theresa May of “kissing up to Arab regimes.”
These inauthentic articles did not last for long. Most of them, and their hosting domains, were ephemeral. Some remained up for only a few days. In most cases, the article would be available for a short while, then taken down, with the link redirecting to the homepage of the real website it was spoofing.
- 1u/elianabadawi, “Nick Clegg: Theresa May attempt to get away with Brexit consequences by 'kissing up to Arab regimes' in vein,” Reddit, April 12, 2017, https://www.reddit.com/r/unitedkingdom/comments/64x217/nick_clegg_theresa_may_attempt_to_get_away_with/.
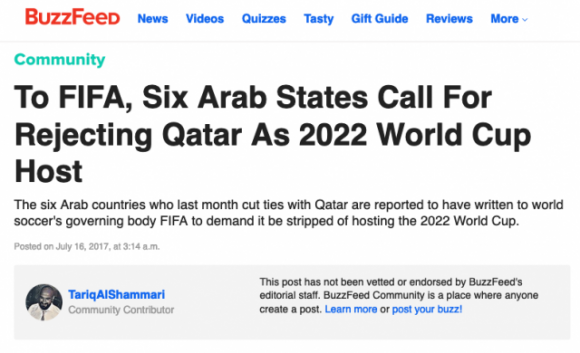
Around April 2017, the six Twitter accounts went quiet and were either deleted (as was the case with @PSJCommunity) or simply stopped tweeting. Soon four new Twitter accounts emerged, also posing as journalists and activists.1 Like the earlier personas, they tweeted links to inauthentic articles, again spoofing real media outlets and quickly deleted and redirected after publication. These new personas also started posting content under their own names across other platforms and open editorial platforms such as Medium,2 Buzzfeed Community (see figure 3 below),3 and OpenDemocracy.4 In some cases, they would link or cite the inauthentic articles as evidence.
- 1Lim et al., “Burned After Reading.” See “Appendix A: Timeline of The Endless Mayfly Network.”
- 2“Tariq AlShammari,” Medium [persona’s author profile on Medium], archive accessed August 12, 2020, https://perma.cc/E22G-ZVPU.
- 3“To FIFA, Six Arab States Call For Rejecting Qatar As 2022 World Cup Host,” Buzzfeed Community [self-published article by the persona Tariq Al-Shammari], archive accessed August 12, 2020, https://perma.cc/X63R-9T2L.
- 4“Yair Netanyahu: a scandalous man,” OpenDemocracy [published by persona Tariq Al-Shammari], archive accessed August 12, 2020, https://perma.cc/53SX-QFY4.
Figure 3: Example of a Buzzfeed Community post one of the Endless Mayfly personas wrote. Source: https://perma.cc/X63R-9T2L.
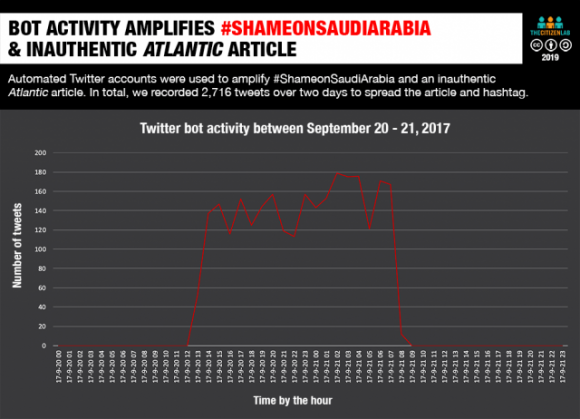
There was also one noted instance of activity that looked like attributed to Endless Mayfly. Between September 20 and September 21, 2017, a large number of accounts on Twitter tweeted a hashtag critical of Saudi Arabia, #ShameOnSaudiArabia. These hundreds of Twitter accounts had usernames made up of a random string of numbers and profiles that were thin (i.e. very little content and activity). In total, there were over 5,500 tweets and retweets with this hashtag.1 Of this activity, 2,716 tweets included a link to an inauthentic Atlantic article, again engaging in by using the domain theatlatnic.com.2
- 1Lim et al., “Burned After Reading.” See “Twitter Bots Disseminate & Amplify Content” section.
- 2“A shocking document shows the shameful acts of Saudis and Emiratis for hiding human rights abuses in Yemen,” theatlatnic.com [inauthentic website purporting to be The Atlantic], archive accessed August 12, 2020, http://archive.is/JNbgJ.
A separate network that has been linked to Iran helped amplify the inauthentic articles identified from Endless Mayfly between 2016 and 2018 and the false allegations within them.1 Of the top 10 domains that most frequently referenced the inauthentic articles, eight (IUVM Press, Whatsupic, AWDNews, Yemen Press, Instituto Manquehue, and RealNienovosti.com) all share the same IP address or registration details, indicating they may be controlled by this same actor.2 There is no overlap in registration information or IP addresses between Endless Mayfly and the allegedly Iranian republishing network, however. As such, it is unclear if they were operated by the same individuals.
By late 2018 there was a lull in activity as the known personas went quiet. However there was one notable instance when a “Mona A. Rahman” reached out to Saudi critic Ali Al Ahmed (see figure 5 below). As previous Endless Mayfly personas had done, she tried to get him to cover a false inauthentic article, this time a spoofed story made to look like it came from the Harvard Belfer Center.
- 1“Suspected Iranian Influence Operation Leverages Network of Inauthentic News Sites & Social Media Targeting Audiences in U.S., UK, Latin America, Middle East,” FireEye, August 21, 2018, https://www.fireeye.com/blog/threat-research/2018/08/suspected-iranian-influence-operation.html.
- 2Lim et al., “Burned After Reading.” See “Iran-linked News Sites Propagate Falsehoods.”
Figure 5: Screenshot of a Tweet by persona “Mona A. Rahman” reaching out to known Saudi critic Ali Al Ahmed. Tweet archived here: https://web.archive.org/web/20181206171532if_/https://twitter.com/mona_….
STAGE 3: Responses by Industry, Activists, Politicians, and Journalists
Because the inauthentic articles were seeded off and on for multiple years, responses from journalists and politicians came at varying times through this period. Therefore, stages 2 and 3 overlapped throughout this network’s known operational lifetime.
In 2017, researchers at Citizen Lab noticed the “Eliana Badawi” persona, who had posted a false Independent article to Reddit in April 2017. Using this article and “Eliana Badawi” as a starting point,1 researchers were then able to monitor for activity and compile datasets of personas, articles, and domains that formed the activity of Endless Mayfly. Citizen Lab realized that many of these seemingly unconnected websites were part of a network.
The total scale of Endless Mayfly’s operation is unclear, but Citizen Lab identified 135 articles across 72 domains and 11 personas by identifying overlaps in domain registration information and Twitter activity (specifically sharing links to the spoofed domains and inauthentic articles).2 For example, the email address jackson.mariani[@]mail.ee was also used to register nationalepost[.]com, foriegnpolicy[.]net and theglobeandmail[.]org. By comparing overlapping WHOIS registration information they were able to connect the different domains, and show coordinated activity. Other examples of Endless Mayfly lookalike websites that took advantage of typosquatting include policito.com,3 which spoofed politico.com, and theguaradian.com, which spoofed theguardian.com.4
Until Citizen Lab published their on Endless Mayfly in 2019, the different spoofed websites, personas, and their inauthentic articles were not formally linked together. As such, any identification and of the typosquatted domains and their inauthentic articles was isolated. Furthermore, some outlets and politicians fell for the ruse, resulting in media exposure, and muddying the waters around certain events.
For example, a spoofed Le Soir article falsely alleging more than 30% of Emanuel Macron’s campaign was funded by the Saudi government received quite a bit of attention from mainstream press and French politicians in March 2017.5 The story circulated among some French-language far-right sites and was tweeted out by Marion Maréchal-Le Pen, a member of parliament for the far-right National Front party in France.
Another instance where mainstream press reported on the false content occured in June, 2017, when Reuters falsely reported that the six Arab countries who had cut ties with Qatar amid an ongoing diplomatic crisis had written to FIFA to demand Qatar be replaced as the host of the 2022 World Cup.6 This was based on a fake article purporting to be by Swiss media outlet, The Local, which researchers later tied to the Endless Mayfly group.7 However, by the time the deceptive article was called out, several other media outlets, such as The Jerusalem Post,8 Haaretz,9 and Global News Canada had reported the same story.10 Reuters later retracted the story.11
Similarly, in late July, 2017, a spoofed Haaretz article falsely claimed that family members of Azerbaijani President Ilham Aliyev had invested some $600 million of personal wealth into the Israeli stock exchange. When the false article disappeared, Armen Press, an Armenian-focused media outlet, alleged Haaretz had deleted it due to its “scandalous” nature and implied the Azerbaijan government may have had a hand in pulling down the article.12 The false article provoked Israel’s ambassador to Azerbaijan to officially refute the allegations in the fake article, believing it to be an authentic Haaretz article.13
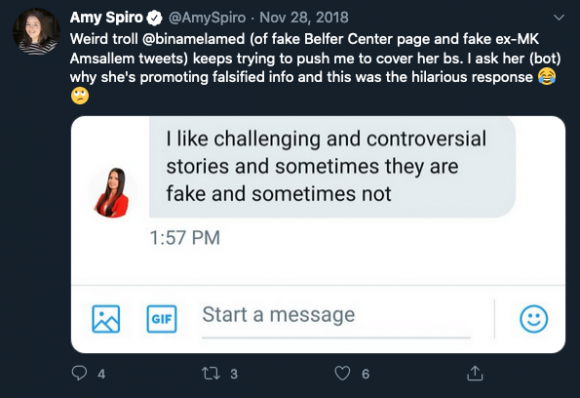
Some journalists called out attempts by Endless Mayfly to seed false stories. Washington Post journalist Anne Applebaum had intimated that one of the articles may have been a Russian influence operation on March 31, 2017.14 Buzzfeed News on August 15, 2017 also reported on a few of the false articles, but pointed to Russia as potentially being behind them.15 Other journalists, who had been contacted by Endless Mayfly personas, also called them out for their suspicious behavior (see figure 6 below for an example).16 ,17
- 1Eliana Badawi (@eliana_badawi), “Clegg: Theresa May’s trip to KSA politically motivated, in line with Arab regimes’ interests,” Twitter, April 5, 2017, https://perma.cc/D7KE-K39V.
- 2Lim et al., “Burned After Reading.” See “Appendix B: Domain Infrastructure” and “Appendix D: Campaign dataset.”
- 3“New evidence for condemning Saudi Arabia in favor of 9/11 bill,” Policito.com [fake Politico site], archive accessed August 12, 2020, https://web.archive.org/web/20161019150309/http://www.policito.com/2016/10/chuck-grassley-I-have-new-evidence-supporting-9-11-bill/.
- 4Craig Silverman and Jane Lytvynenko, “How A Hoax Made To Look Like A Guardian Article Made Its Way To Russian Media,” Buzzfeed News, August 15, 2017, https://www.buzzfeednews.com/article/craigsilverman/how-a-hoax-made-to-look-like-a-guardian-article-made-its.
- 5Adrien Sénécat, “Macron « financé par l’Arabie saoudite » : une intox massivement relayée par l’extrême droite,” Le Monde, March 2, 2017, https://www.lemonde.fr/les-decodeurs/article/2017/03/02/macron-finance-par-l-arabie-saoudite-une-intox-massivement-relayee-par-l-extreme-droite_5088356_4355770.html.
- 6Mitch Phillips, “Boycott nations demand FIFA strips Qatar of 2022 World Cup - report,” Reuters, July 16, 2017, https://www.reuters.com/article/ozasp-uk-soccer-worldcup-qatar-idAFKBN1A1070-OZASP.
- 7“The Local victim of Qatar fake news plant,” The Local, July 16, 2017, https://www.thelocal.ch/20170716/the-local-victim-of-qatar-fake-news-plant.
- 8“Report: Arab countries urge FIFA to drop Qatar as 2022 World Cup host,” The Jerusalem Post, July 16, 2017, https://www.jpost.com/Middle-East/Report-Arab-countries-urge-FIFA-to-drop-Qatar-as-2022-World-Cup-host-499835.
- 9“Qatar Crisis: Boycotting Arab States Ask FIFA to Stop Doha's 2022 World Cup Over 'Terrorism',” Haaretz, July 16, 2017, https://www.haaretz.com/middle-east-news/arab-states-ask-fifa-to-bar-qatar-from-hosting-2022-world-cup-1.5494372.
- 10“Report of Arab countries asking FIFA to strip Qatar of World Cup fake: Swiss news site,” Global News, July 15, 2017, https://globalnews.ca/news/3601764/saudi-arabia-qatar-world-cup/.
- 11“Advisory - Boycott nations demand FIFA strips Qatar of 2022 World Cup: report,” Reuters, July 16, 2017, https://uk.reuters.com/article/uk-soccer-worldcup-qatar/advisory-boycott-nations-demand-fifa-strips-qatar-of-2022-world-cup-report-idUKKBN1A00QM.
- 12Article disclosing Aliyev family’s secret activity removed from Israeli 'Haaretz' website,” ArmenPress, August 3, 2017, https://armenpress.am/eng/news/900721/article-disclosing-aliyev-family%E2%80%99s-secret-business-activity-removed-from-israeli-haaretz-website.html.
- 13“Israel's ambassador to Azerbaijan refutes the article published in Haaretz newspaper,” Azvision.az, July 31, 2017, https://en.azvision.az/news/70032/israels-ambassador-to-azerbaijan-refutes-the-article-published-in-haaretz-newspaper.html.
- 14Anne Applebaum, “Every day a new Russian revelation. That’s not as bizarre as it sounds,” The Washington Post, March 31, 2017, https://www.washingtonpost.com/opinions/global-opinions/every-day-a-new-russian-revelation-thats-not-as-bizarre-as-it-sounds/2017/03/31/93f787dc-161b-11e7-9e4f-09aa75d3ec57_story.html.
- 15Silverman and Lytvynenko, “How A Hoax Made To Look Like A Guardian Article Made Its Way To Russian Media.”
- 16Lahav Harkov, “Who is creating fake news sites to slander Liberman and Netanyahu?,” The Jerusalem Post, November 14, 2018, https://www.jpost.com/Israel-News/Who-is-creating-fake-news-sites-to-slander-Liberman-and-Netanyahu-571923.
- 17Marine Buisson, “«Le Soir» victime d’un plagiat autour d’une information sur Macron,” Le Soir, February 3, 2017, https://plus.lesoir.be/84349/article/2017-03-02/le-soir-victime-dun-plagiat-autour-dune-information-sur-macron.
Figure 6: Amy Spiro, a journalist for The Jerusalem Post, calls out one of the network’s persona who attempted to share a near identical copy of a Harvard Belfer Center website. Source: https://twitter.com/AmySpiro/status/1067751723446489088.
STAGE 4:
Despite these isolated attempts to debunk and reveal activities linked to “Endless Mayfly”, the network was not exposed publicly until Citizen Lab released a research report linking the personas and domains together on May 14, 2019.1 The report received some mainstream press coverage,2 including by media outlets who had been targeted, such as The Atlantic3 and The Jerusalem Post.4
Separately, the Iran-linked media network that was used in Stage 2 to amplify Endless Mayfly content was also identified as engaging in “coordinated inauthentic behavior” by investigations from Twitter,5 ,6 and .7 As such, hundreds of accounts were deleted or suspended and their associated content removed, which included some personas connected with Endless Mayfly. But because there are no overlapping accounts, there is not enough evidence to state whether this Iranian-linked media network was working with or the same operators behind Endless Mayfly. This media network, however, did help Citizen Lab conclude that Endless Mayfly was most likely Iran-aligned, along with other indicators such as narrative and content analysis from the articles’ content and the personas’ Twitter activity.8
STAGE 5: Adjustments by Manipulators to New Environment
It’s unclear whether the operators shifted tactics or continued after widespread coverage of their activities, however throughout their known operational lifetime it appears they were experimenting with different tactics. For example, the first six known personas were affiliated with a made-up NGO but eventually the NGO and those personas were abandoned in favor of new personas. These new personas still disseminated inauthentic articles on typosquatted domains, but also engaged in different tactics, such as publishing on Medium or BuzzFeed Community.
Since 2019, however, it remains unclear how the operation as a whole evolved or whether it is still ongoing. Reports of similar activity emerged in August, 2020 with speculation that it may be linked to Endless Mayfly.9 However, without any evidence beyond the observed tactics, it remains unclear whether the activity’s origins are the same.
- 1Lim et al., “Burned After Reading.”
- 2Scott Shane and Ronen Bergman, “New Report Shows How a Pro-Iran Group Spread Fake News Online,” The New York Times, May 14, 2019, https://www.nytimes.com/2019/05/14/world/middleeast/iran-fake-news-report.html.
- 3Alexis C. Madrigal, “The Telltale Signs of a Fake Atlantic Article,” The Atlantic, May 15, 2019, https://www.theatlantic.com/technology/archive/2019/05/how-spot-irans-fake-news-disinformation-campaign/589438/.
- 4Lahav Harkov, “Iranian disinformation campaign targeted Israelis,” The Jerusalem Post, May 14, 2019, https://www.jpost.com/middle-east/iranian-disinformation-campaign-targeted-israelis-589633.
- 5Twitter Safety (@TwitterSafety), “Working with our industry peers today, we have suspended 284 accounts from Twitter for engaging in coordinated manipulation. Based on our existing analysis, it appears many of these accounts originated from Iran.,” Twitter, August 21, 2018, https://twitter.com/TwitterSafety/status/1032055161978585088.
- 6“Taking Down More Coordinated Inauthentic Behavior,” Facebook, August 21, 2018, https://about.fb.com/news/2018/08/more-coordinated-inauthentic-behavior/.
- 7Kent Walker, “An update on state-sponsored activity,” Google, August 23, 2018, https://blog.google/technology/safety-security/update-state-sponsored-activity/.
- 8Gabrielle Lim, “Case study: Attributing Endless Mayfly” in Verification Handbook: For Disinformation And Media Manipulation, ed. Craig Silverman (European Journalism Centre, 2020), https://datajournalism.com/read/handbook/verification-3/investigating-platforms/11a-case-study-attributing-endless-mayfly.
- 9Adam Rawnsley, “Pro-Iran Troll Posed as WHO Official to Push Racist Coronavirus Hoax,” The Daily Beast, August 11, 2020, https://www.thedailybeast.com/pro-iran-troll-posed-as-who-official-to-push-racist-coronavirus-hoax.
Cite this case study
Gabrielle Lim, "Copycat Websites: The Endless Mayfly Network," The Media Manipulation Case Book, July 15, 2022, https://casebook-static.pages.dev/case-studies/copycat-websites-endless-mayfly-network.