The Life Cycle Method for Understanding and
The media manipulation life cycle (MMLC) forms the basis of the Casebook, giving a common framework for journalists, researchers, technologists, and members of to understand the origins and impacts of disinformation and its relation to the wider information ecosystem.1 Situated in the emerging field of Critical Internet Studies,2 this research methodology combines social science and data science to create a new framework for studying systems and their vulnerabilities.3
Selection Criteria
Media manipulation case studies should explain an emergent socio-technical phenomenon that involves using the affordances of information and communication technologies to hide or otherwise conceal the identities of actors, the behavior of groups, and/or the accuracy of content. The Casebook aims to provide users with a wide range of cases from around the world that illustrate how specific social conditions and features of technology can be used to manipulate the information ecosystem, leading to the disruption of public understanding of political or scientific issues.
Cases are selected based on three main criteria: the novelty of tactics and strategies; the scale of the operation and its resulting outcomes and institutional responses; and whether there is enough high-quality empirical evidence. To identify whether or not a case should be included in Casebook, we ask the following questions:
Novelty
Goal: To increase diversity of analysis within the Casebook
- Does this case expand the diversity of strategies and tactics used in our cases?
- Does this case introduce a new or original tactical mix in executing a strategy?
- Are the social and technical vulnerabilities being exploited in new or different ways?
- Are there novel targets, campaign operators, or participants involved in the case?
- Did the campaign operators or participants adjust their tactics in response to institutional actions (ex. user ban, , )?
Scale
Goal: To include cases with observable outcomes and discernable patterns of engagement
- What is the scale of media coverage (low, medium, high)?
- Does this case have low, medium or high user engagement (ex. retweets, comments, likes)?
- Does this case span multiple platforms, if so how many?
- Did this case invoke institutional responses (ex. political response, , change in platform governance)?
Evidence
Goal: To ensure cases are backed by high-quality sources and multiple indicators
- Is there enough evidence to support analyses of the tactics and strategies employed?
- Are the secondary sources reliable and/or drawn from high-quality investigations? (ex. academic research or credible investigative reporting)
- Is the data collection and analysis repeatable by other researchers?
Methods
The means for documenting case studies require a variety of methods that span qualitative inquiry, quantitative analysis, content analysis, network mapping, process tracing, and ethnographic studies. As such, a variety of indicators from different sources (e.g., commercial threat reporting, platform reporting, independent research, investigative journalism, public statements, website scraping) will be used to triangulate findings. In addition, each case study will vary in the methods used to detect and document media manipulation campaigns, depending on how the case developed. All source material will be presented and cited, and when possible, archived and persevered.
For more information on the life cycle model, selection criteria, coding process, and research methods, please refer to our code book and our primer on investigative digital ethnography.
Investigative Digital Ethnography
The Media Manipulation Life Cycle
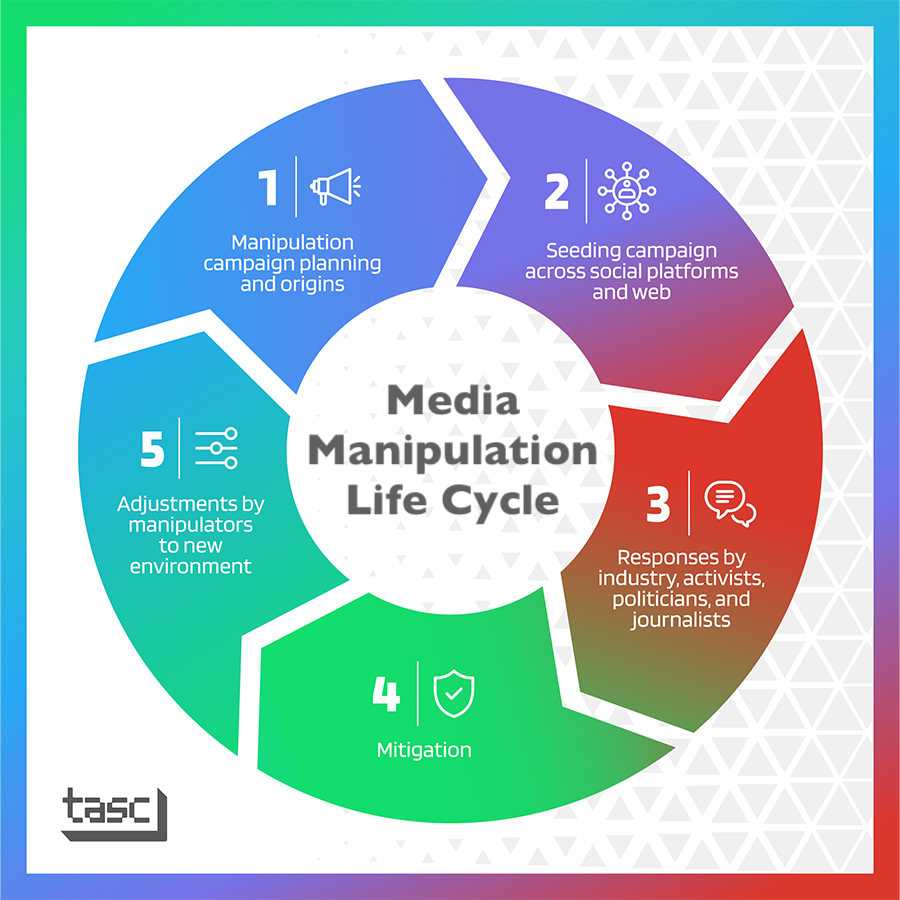 Each case is written according to the five stages defined in the MMLC, allowing researchers to analyze the order, scale, and scope of the campaign in question, as well as the actors involved, platforms used, vulnerabilities (both social and technical) exploited, and outcomes.
Each case is written according to the five stages defined in the MMLC, allowing researchers to analyze the order, scale, and scope of the campaign in question, as well as the actors involved, platforms used, vulnerabilities (both social and technical) exploited, and outcomes.
Stage 1: Manipulation campaign planning and origins
The first stage documents the origins or planning stage of a campaign and is generally limited to conversations by a small group of operators or campaign participants, who develop narratives, images, videos, or other material to be spread online as “evidence.” In effect, Stage 1 details the intended strategies, tactics, and goals of the campaign.
Stage 2: Seeding the campaign across social platforms and web
Stage 2 documents the tactics and relevant materials used to execute the campaign. In other words, this stage details the dissemination and propagation of content relevant to the operation.
Stage 3: Responses by industry, activists, politicians, and journalists
After content has been seeded, the campaign moves on to Stage 3, which documents how actors and organizations outside the campaign (e.g., civil society organizations, politicians, political parties, mainstream ) react. The third stage of the operation is usually a turning point indicating whether the campaign was effective in gaining attention via amplification or if it led to another observable outcome.
Stage 4:
The fourth stage of a manipulation campaign documents actions by tech companies, government, journalists, or civil society to mitigate the spread of a campaign’s content, messaging, and effects.
Stage 5: Adjustments by manipulators to new environment
The fifth stage of a manipulation campaign involves how the operators and campaign participants adapt according to mitigation efforts described in Stage 4 and the resulting changes in the information ecosystem.
- 1Joan Donovan, “The Life Cycle of Media Manipulation,” in The Verification Handbook 3, 2020, https://datajournalism.com/read/handbook/verification-3/investigating-d….
- 2Amelia Acker and Joan Donovan, “Data Craft: A Theory/Methods Package for Critical Internet Studies,” Information, Communication & Society 22, no. 11 (September 19, 2019): 1590–1609, https://doi.org/10.1080/1369118X.2019.1645194.
- 3Matt Goerzen, Elizabeth Anne Watkins, and Gabrielle Lim, “Entanglements and Exploits: Sociotechnical Security as an Analytic Framework,” in 9th USENIX Workshop on Free and Open Communications on the Internet (FOCI) (Santa Clara, CA, 2019), https://www.usenix.org/conference/foci19/presentation/goerzen.
